How to evaluate AI coding tools for enterprise teams
MAR. 4, 2026
4 Min Read
You should pick AI coding tools using measurable goals, strict controls, and a controlled pilot.
Enterprise teams get value from AI code editors when the tools reduce cycle time without raising defect rates, security risk, or review burden. A randomized study found developers using an AI assistant completed a coding task about 55% faster. That gain disappears if teams accept low-quality code, create policy exceptions, or generate work your senior engineers must undo. Evaluation has to treat AI coding tools like production-grade software, not a personal plugin choice.
The strongest enterprise AI coding tools selection process starts with outcomes and constraints, then tests workflow fit, safety, and quality under your standards. Teams that start with feature checklists tend to miss the hidden costs in review time, compliance work, and rework after deployment. You’ll get better results when you define success metrics up front and run the same tool through a repeatable set of checks. That approach also makes it easier to align executives, data leaders, and tech leaders on a choice that stands up under scrutiny.
key takeaways
- 1. Start with measurable goals that balance cycle time, code quality, and security risk, then hold every tool to the same baseline metrics.
- 2. Filter options using non-negotiable enterprise requirements for identity, data handling, auditability, and workflow fit across IDEs, repos, code review, and CI.
- 3. Use a controlled pilot to validate quality and cost, then lock in governance so productivity gains persist without policy exceptions.
Set evaluation goals tied to code quality, speed, and risk

Set goals that balance throughput with code health and operational risk. Track a small set of measures you can verify, such as time from ticket start to merge, code review iteration count, defect escape rate, and security finding volume. Put each metric on a baseline before any rollout. Treat “more code” as a warning sign, not a win.
Start with two or three target workflows where speed matters and the output is easy to inspect, such as routine refactors or test creation. Define what “good” means in observable terms, like fewer review comments per pull request and stable post-release incident rates. Add one red-line risk metric, such as any increase in secrets leakage or policy violations, so the evaluation has a hard stop. Align those measures with how your leadership team reports delivery performance today, so results stay credible.
Goals also need ownership, or they turn into opinion battles. Assign a product owner for the evaluation and a technical owner for measurement and tooling. Require the same standards you already use for code review and continuous integration (CI), so the tool is judged within your delivery system. Teams that do this early avoid spending months debating “developer happiness” while ignoring defects and compliance work.
"The winning tool will produce code that reviewers can trust, not code that looks polished at first glance."
Define must have requirements for enterprise AI coding tool use
Must-have requirements define what the tool must support before you assess “best” features. Cover identity and access, data handling, deployment options, language coverage, and auditability. Write requirements as testable statements, not vendor promises. Procurement and security reviews will move faster when requirements are specific.
Translate requirements into checks your team can run in days, not weeks. Confirm how the tool handles prompts, code context, and telemetry, and require clear retention controls. Validate that users authenticate through your standard identity provider and that access can be limited by role. Require an admin layer that supports policy configuration and reporting, not just end-user settings.
| Evaluation checkpoint | What passing looks like when you verify it |
|---|---|
| Identity and access control | Sign-in uses your SSO and access can be limited by role. |
| Prompt and code data handling | Retention, storage location, and reuse policies are explicit and enforceable. |
| Audit and reporting | Admins can review usage, policy overrides, and key events without manual log work. |
| Language and framework coverage | The tool performs well on the languages you ship and maintain. |
| Deployment and network controls | Traffic paths and egress controls match your security architecture requirements. |
Requirements should also clarify what you will not allow. Put guardrails on use with regulated data, proprietary algorithms, and unreleased product details. Decide if the tool can be used only in approved repositories or on managed devices. When these rules are written before trials start, you’ll avoid a shadow rollout that forces a painful rollback later.
Check workflow fit across IDEs, repositories, code review, and CI
Workflow fit decides adoption and long-term cost. The tool must work across your supported IDEs and pair cleanly with your repository, branching model, and CI checks. If suggested code creates extra review churn, speed gains vanish. Evaluate the full path from edit to merge, not just autocomplete quality.
A practical check is to run the tool through one end-to-end work item using your normal processes. A team working on a Java service might use the tool to draft a new endpoint plus unit tests, then run the same linting, dependency scanning, and pull request review rules used for any change. Reviewers can then compare how many comments, revisions, and follow-up fixes the AI-assisted change required versus a typical change. That single exercise reveals friction points that demos hide.
Workflow fit also includes collaboration and consistency. Confirm that the tool supports shared settings so teams can standardize prompts, guardrails, and formatting rules. Check that it behaves predictably when multiple files and repository context are involved, since partial context often produces confident but wrong changes. If the tool can’t respect your coding standards in review, it will add cost even when it feels fast.
Assess security, privacy, and compliance for prompts, code, and logs
Security review must treat prompts, code snippets, and logs as sensitive data. Verify where data goes, who can access it, how long it is retained, and how it is protected in transit and at rest. Confirm controls for admin policy, user access, and audit. A tool that cannot prove these basics will fail at scale.
Focus on the failure modes your CISO team worries about, not generic checklists. Data leakage can happen through pasted secrets, copied stack traces, or prompts that include customer identifiers. Prompt injection also matters when tools read repository files or internal docs, because untrusted text can manipulate output. Require clear documentation for isolation boundaries, retention settings, and incident response support, so the tool fits your security operating model.
Compliance needs clear ownership and repeatable evidence. Map the tool’s controls to your internal policies for regulated data, logging, and third-party risk. Confirm legal terms on training and reuse of customer code context, and ensure they match your IP posture. Security and compliance should finish as a signed decision, not a set of “known issues” that linger through rollout.
"Evaluation has to treat AI coding tools like production-grade software, not a personal plugin choice."
Test output quality with benchmarks, review rubrics, and acceptance rates
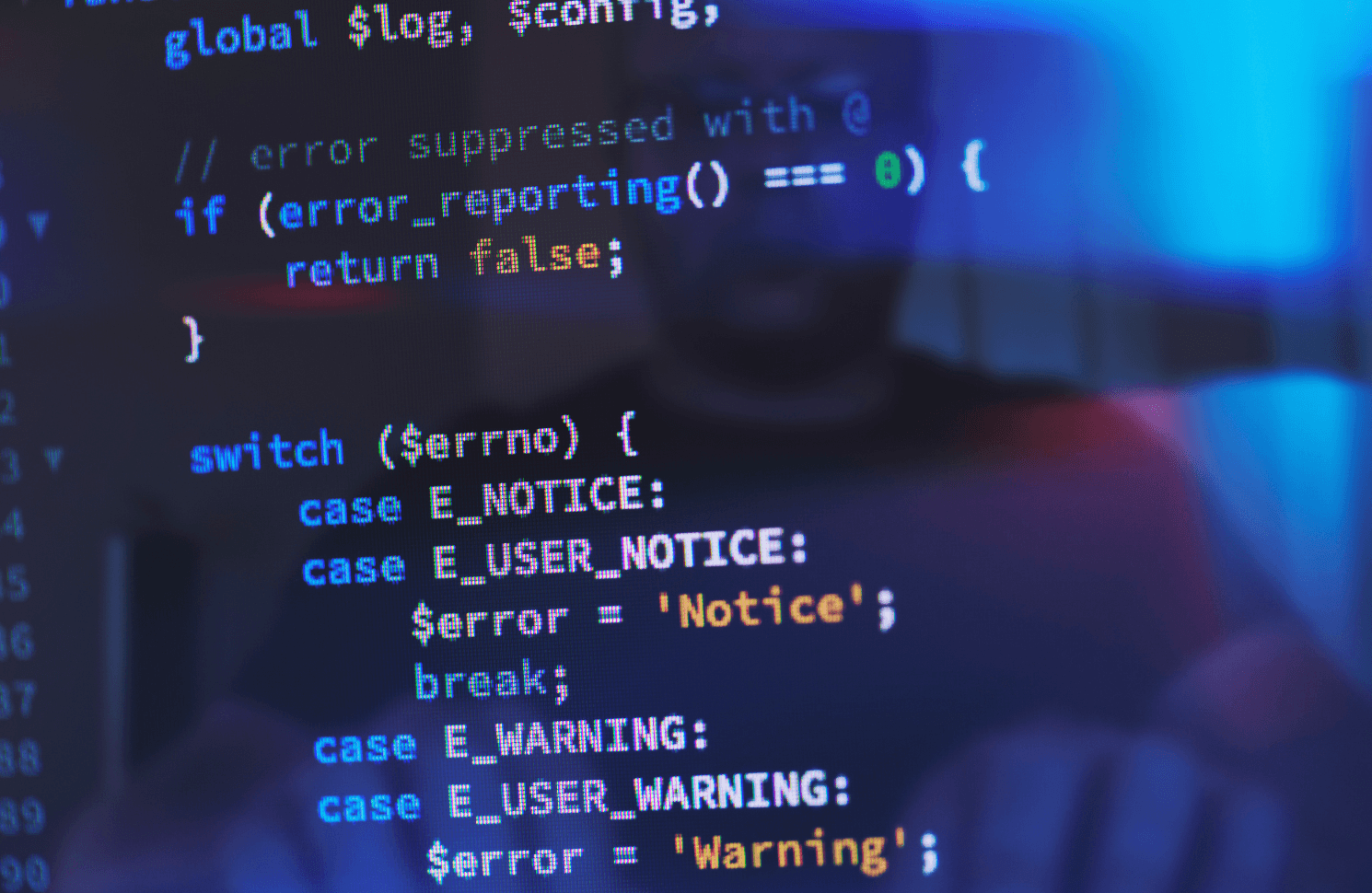
Quality testing should score AI output the same way you score any code. Use a small benchmark set that reflects your codebase patterns, then grade suggestions against a review rubric for correctness, readability, and maintainability. Track acceptance rate and the rework needed after acceptance. High acceptance with high rework is still a loss.
Quality matters because defects are expensive and they compound over time. Software defects have been estimated to cost the U.S. economy $59.5 billion each year. A tool that increases defect escapes, even slightly, can erase any productivity gain through incident response and patch cycles. Your evaluation should include tests, static analysis, and security scanning outcomes, not just reviewer impressions.
Make the rubric simple enough that teams will use it. Require reviewers to label the reason for rejection, such as “wrong logic,” “breaks style,” “adds risk,” or “unclear.” Compare AI-assisted pull requests to normal pull requests on the same team to avoid false comparisons across teams. The winning tool will produce code that reviewers can trust, not code that looks polished at first glance.
Estimate total cost of ownership and expected productivity lift
Total cost of ownership includes more than licenses. Add admin time, security review effort, policy management, training, and the infrastructure needed for logs and reporting. Estimate productivity lift using your own delivery metrics, not vendor claims. A tool that looks cheap per seat can be expensive per merged change.
Build a simple ROI model that finance and engineering can both accept. Translate time saved into cost saved only when it reduces cycle time or frees capacity for higher-value work, not when it just produces more activity. Include the cost of higher review time if the tool increases revisions or adds security findings. Treat risk reduction as a benefit only when you can tie it to fewer incidents, fewer escalations, or fewer compliance exceptions.
Execution details also change TCO (total cost of ownership), especially at enterprise scale. Lumenalta teams often see the biggest cost swings come from governance overhead, not licensing, once usage spreads beyond early adopters. Standardizing policies, prompt practices, and measurement keeps operational load predictable. If you can’t run the tool with stable controls, TCO will rise even if developer sentiment stays high.
Run a controlled pilot and set ongoing governance and controls
A controlled pilot turns tool selection into evidence you can act on. Define a short pilot window, restrict it to a few teams, and measure the goals you set at the start. Lock down policy, logging, and access before expanding use. Treat the pilot as a production readiness check, not a feature trial.
Keep the pilot simple, and make it hard to game. Pick work that represents your normal mix of maintenance and delivery, not a showcase project. Require reviewers to apply the same standards as usual, and record outcomes in a shared scorecard. Use a small checklist so every team runs the pilot the same way.
- Define success metrics and a baseline before the pilot starts
- Limit scope to approved repos and managed developer devices
- Apply standard CI checks and code review rules
- Log usage and policy events with an owner for follow-up
- Decide go or no-go using measured results
Governance is the part teams skip, then regret. Set rules for where the tool can be used, how prompts should be written, and what code must never be shared. Assign owners for policy, measurement, and vendor management so controls don’t decay after the first rollout. Lumenalta engagements work best when governance is treated as a delivery capability, not paperwork, because that discipline keeps productivity gains without letting risk creep into your SDLC.
Table of contents
- Set evaluation goals tied to code quality, speed, and risk
- Define must have requirements for enterprise AI coding tool use
- Check workflow fit across IDEs, repositories, code review, and CI
- Assess security, privacy, and compliance for prompts, code, and logs
- Test output quality with benchmarks, review rubrics, and acceptance rates
- Estimate total cost of ownership and expected productivity lift
- Run a controlled pilot and set ongoing governance and controls
Want to learn how Lumenalta can bring more transparency and trust to your operations?